IT Governance & Risk Management Best Practices for Enterprise Leaders
Contents
Contents
Every technology leader is expected to manage a set of operational tensions that are somewhat contradictory. Ship more features and strengthen security. Scale systems and maintain compliance. Trading one for the other creates dangerous blind spots in oversight and risk visibility, often leading to expensive project overruns and a disconnect between high-level strategy and what is actually happening in production.
With IT governance and risk management in place, you don’t have to choose between rapid iteration and security posture. You can have both. Moreover, implementing governance — starting with a thorough IT risk assessment — allows enterprises to increase resilience across the entire IT lifecycle.
In practice, effective governance boils down to two core principles: managing risk early and making decision logic visible. The approach below addresses both: reducing blind spots and building the credibility needed to move forward with the transformation.
Why Is IT Governance and Risk Management Crucial for Modern Enterprises
As organizations expand and become risk-bearing entities, they inevitably hit a resilience threshold. Informal check-ins and shared trust that worked for a small team of ten product and engineering leaders fracture under the weight of multi-team delivery and distributed cloud architectures. At this stage, enterprise IT governance ceases to be a formal administrative requirement and becomes a survival mechanism for sustaining coordinated execution.
The real value of mature governance lies in its ability to make engineering culture proactive and more resilient. Consider a mid-sized enterprise scaling its cloud infrastructure. The team ships code, discovers a security vulnerability, and drops everything to combat a weakness. This is a reactive cycle prone to recurring disruptions and roadmap instability.
In a proactive culture supported by IT governance best practices, that same team integrates cloud architecture patterns that support continuous delivery with automated compliance guardrails. Potential risks are flagged during the project lifecycle long before they appear in audit trails or customer complaints.
To put it together, we can outline the structural advantages, or rather operational leverage organizations realize by adopting governance practices:
- Minimized decision debt. Effective governance reduces uncertainty in critical decisions. Instead of making high-pressure architectural choices in a vacuum, you align technical moves with long-term strategic IT alignment, preventing costly legacy traps down the road.
- Predictable delivery momentum. The PMO (Project Management Office) can identify cross-team dependencies and solve bottlenecks before they cause project delays or contractual penalties.
- Automated guardrails. Implementing governance enables teams to embed compliance and security checks into their deployment pipelines as Policy-as-Code (PaC). You can translate regulatory compliance (GDPR, SOC2) into scripts that automatically block deployments if certain security requirements are not met.
- Reinforced digital resilience. A robust risk assessment framework helps you validate the business continuity plan (BCP) and disaster recovery (DR) to prove that the organization can continue to deliver services even during a systemic operational crisis.
- Reducing uncertainty in technical decision-making. When your PMO establishes a transparent track record of risk management, it provides you with the credibility to secure board approval for high-risk initiatives.
How Governance Connects IT Strategy to Business Objectives
Technical teams detached from the organization’s risk appetite tend to solve for the immediate sprint, making isolated choices that may not withstand the first encounter with cross-functional dependencies. They opt for tools with novelty or speed in view. As a result, organizations end up with projects that seem technically ambitious but deliver marginal business value.
Strategic IT alignment serves as a corrective lens that synchronizes every technical choice with business outcomes by clarifying priorities, risk tolerance, and success criteria. This doesn’t mean imposing top-down control. On the contrary, you enable teams to manage their own resource allocation with strategic intent, in the right direction for the product’s long-term viability.
The understanding of why changes behavior. Engineers start considering the business context when selecting a tech stack, and product teams understand which regulatory constraints are essential to customer trust.
To reach this level of organizational alignment, companies should encourage several performance standards:
- Shared KPIs that measure business impact, like customer acquisition cost or time-to-market for revenue-generating features, are more important than deployment frequency.
- Regular alignment checkpoints that validate progress against business-impact metrics and recognize projects that no longer meet acceptable cost-to-value ratios.
- Cross-functional steering committees that engage technical leaders to participate in business planning and add a technical risk perspective before executive teams finalize the commitments.
- Transparent risk tolerance documentation that defines the acceptable risk threshold to achieve faster delivery and specifies the boundaries when thorough oversight must prevail.
As soon as the enterprise arranges all these elements, software project risk mitigation becomes a natural byproduct of the workflow. Teams will stop seeing compliance as an audit obligation they have to meet and start seeing it as the foundation for a stable delivery environment.
The IT Risk Management Lifecycle: From Identification to Continuous Monitoring
As it often happens, annual risk assessments morph into performative documents that reside in shared drives waiting for the next compliance audit. More than a third of enterprises fell victim to security breaches originating within their supply chain, often because nobody monitored vendor access between reviews. Point-in-time evaluations capture risks that existed during that specific window but miss everything that creeps in afterward, be they new dependencies or configuration changes.
The point is that effective IT governance risk management frames risk as a permanent variable rather than an event, and therefore should follow certain phases to ensure nothing is overlooked in the heat of a sprint.
Phase 1. Identification
This step involves searching for threats at every touchpoint of the SDLC, including security scanning tools, architecture reviews and incident retrospectives that reveal latent vulnerabilities in existing deployment pipelines.
Phase 2. Prioritization
Upon cataloging all possible disruptors, big and small, they need to be filtered and triaged against the business context to separate theoretical vulnerabilities from real exposures threatening critical systems or regulatory standing.
Phase 3. Mitigation
The cross-functional team implements controls proportional to risk severity and potential impact, allocating resources judiciously to address critical security gaps and staying on track with the planned trajectory.
Phase 4. Monitoring
This stage is vital to make risk management routine and to track the effectiveness of existing controls amid rapid deployment changes, allowing you to pivot the strategy immediately after deviations happen.
Phase 5. Feedback and Refinement
It’s a mistake to assume that the process that works today will remain relevant tomorrow. That said, refine your risk approaches based on new security revelations and insights.
The difference between lifecycle thinking and periodic assessment shows up in incident response speed. By following an IT risk management framework like ISO 27001 or the NIST framework, organizations can see measurable improvements in threat detection and remediation, as well as faster recovery times.
IT Governance Best Practices That Drive Long-Term Resilience
Effective stakeholder management is one of the invisible drivers behind resilient product evolution. A study found that mature governance in this area can increase the likelihood of a project meeting stakeholder expectations by 30%, primarily by eliminating misalignment and communication gaps, key causes of technical risks.
To build resilience from the ground up, accountability must be hardcoded into the workflow and supported by a number of governance practices.
Ownership Models
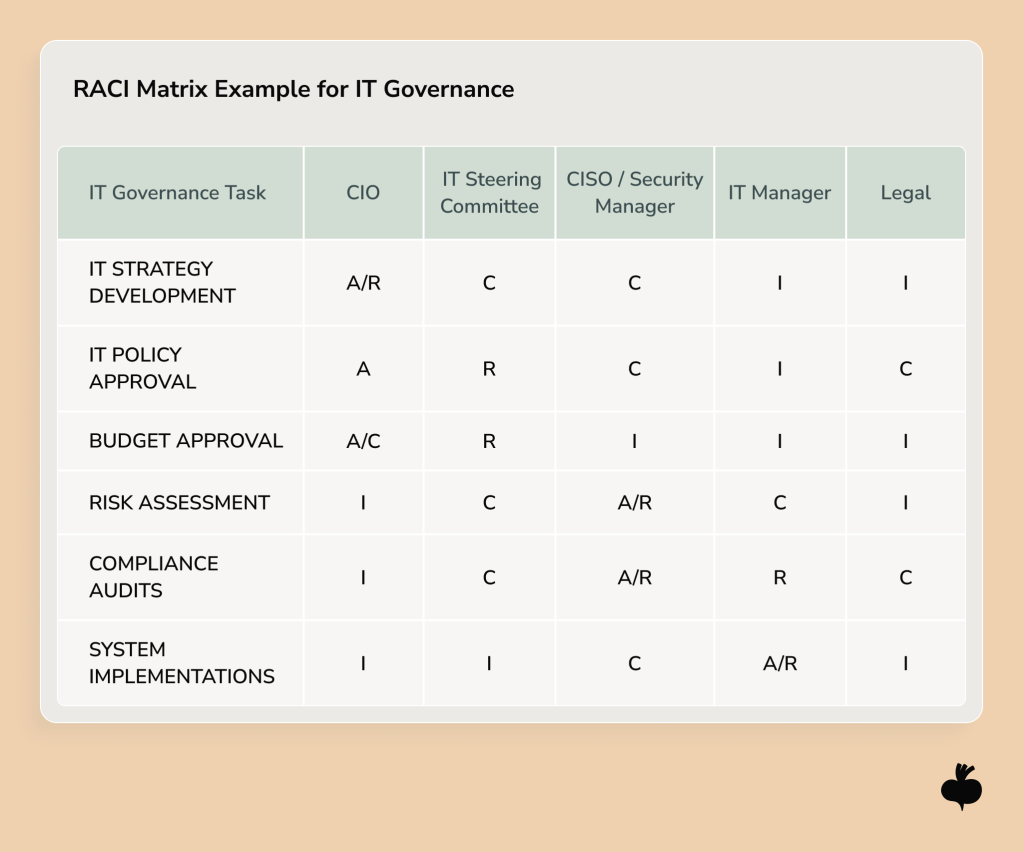
When incidents occur, there must be a responsible person or team to resolve them to avoid ownership being passed from team to team. Many organizations use the RACI matrix (Responsible, Accountable, Consulted, and Informed) to get rid of guesswork and mitigate the risk of tasks falling through the cracks or decisions being delayed due to unclear authority.
Cross-Team Visibility
When DevOps, quality assurance (QA), and product teams have access to the same project data, governance stops feeling imposed from above. This transparency creates vigilance, which in turn encourages teams to catch emerging risks when someone notices an unusual spike in error rates, not because it was accidentally revealed during report preparation for compliance officers.
Response Hierarchy
Teams should understand which decisions they own, which require leadership approval, and how to deal with exceptions to standard processes. Organizations document these paths for common scenarios, so engineers don’t waste time seeking permission for pre-authorized contingency planning measures.
Health Benchmarks
Focus on KPIs that reflect the true cost of risk and quality, such as the ratio of planned vs. reactive work, mean time to recovery (MTTR), percentage of projects delivered within budget, etc. These metrics are more indicative of a team’s ability to show high performance and are better aligned with executive-level goals.
Documentation Discipline
In agile project management, documentation is sometimes reduced to ticket comments. That’s a big omission. Detailed decision logs and audit trails help future teams retrace the logic and troubleshoot anomalies faster.
The mentioned IT project governance best practices don’t prevent all problems. Nevertheless, teams operating under clearly defined governance structures spend less effort negotiating ownership during crises and more capacity on refining delivery processes.
IT Risk Management Best Practices in the Cloud and AI Era
Cloud platforms and AI systems bring new risks that legacy governance frameworks don’t adequately mitigate. Only 26% of surveyed organizations have fully operationalized AI governance policies. The gap between the adoption of cloud and AI technologies and the implementation of risk controls is widening, and signals that most teams are building on shaky foundations that might compromise long-term digital resilience.
When you rely on third-party cloud architecture for continuous delivery, you need to be aware of the provider’s compliance and regional data residency constraints. In this situation, risk management shifts from controlling servers to assessing provider SLAs and tracking resource consumption to set policies around those indicators. Teams looking for green cloud computing or in need to accelerate cloud projects should account for the long-term environmental and financial trade-offs of their infrastructure choices.
Now, AI, the most rapidly adopted and enthusiastically viewed technology among executives, is much more difficult to audit and predict than traditional IT infrastructure. To reconstruct the chain of thought and understand why an AI agent has made a certain decision requires different instrumentation and human-in-the-loop oversight. Teams exploring AI agents vs traditional automation find out that IT risk management best practices must also address behavioral monitoring, drift detection, and explainability requirements.
To develop decent governance, risk, and compliance management is not enough to add approval gates on top of cloud deployments. You need to revise your frameworks and align your risk tolerance. The reality is that modern business continuity plans must cover multi-cloud strategies and AI fallback procedures to ensure that a provider’s outage doesn’t paralyze your core operations.
Common Governance Failures That Lead to Cost Overruns and Security Incidents
It’s common for companies to settle for paper-thin security policies, which creates a dangerous illusion of protection without any of the actual guardrails. That’s far from being the only reason for security incidents.
Below, we outlined the most widespread pitfalls and how to overcome them using IT project management best practices.
Reliance on Lagging Indicators and Gut Feeling
Decisions made based on last month’s billing reports or a manager’s subjective intuition are one of the most frequent causes of project failures. Reckoning on lagging indicators, which only confirm you’ve hit an obstacle, reveals the risk when it’s already too late to prevent loss or damage. To gain control, teams must replace post-facto summaries with current data to guide their processes for risks upfront.
Lack of Strategic Alignment and Resource Prioritization
Inability to align the project portfolio with business objectives leads to resources being allocated to low-impact initiatives while high-value projects remain underfunded. The same applies to risk management, where trivial compliance checks and mission-critical vulnerabilities compete for attention without regard to risk severity. Aligning delivery roadmaps with enterprise risk tolerance is crucial for organizations to maintain business continuity.
Operational Silos
Inconsistent governance across different departments creates functional silos that hide systemic risks. Since not all departments adhere to the same security standards as the rest of the enterprise, that department or system becomes your weakest link that attackers can detect first.
Not to mention that different teams may duplicate initiatives and reporting workflows, increasing the costs of coordination and undermining efficiency.
Frameworks That Support Strong IT Governance and Risk Management
The vast majority of US organizations now use the NIST Cybersecurity Framework (CSF), making it an official gold standard for American businesses, especially after the release of a large-scale update, NIST CSF 2.0, in 2024. Some misinterpret the standard as a plug-and-play solution. In practice, NIST, along with other frameworks, should be a guiding compass calibrated to an organization’s maturity and tech stack.
Let’s first get on the same page regarding the most well-known frameworks and their governance dimensions:
- NIST CSF – a risk-based approach organized around five core functions: Identify, Protect, Detect, Respond, Recover, primarily used by federal agencies and critical infrastructure providers.
- SOC 2 is an attestation framework for SaaS companies and cloud-based startups looking to prove their operational integrity. It validates that a service provider’s controls cover security and data privacy.
- ISO 27001 is an international standard for information security management systems with specific control requirements and certification processes adopted by global organizations and B2B service providers.
Back to the effective IT governance, risk, and compliance management, blindly adhering to all the framework’s prescribed controls. What high-performing organizations do is cherry-pick relevant controls to mitigate their most acute risks and modify processes to match operational reality and delivery model. In short, the best practice is disciplined customization.
Case Scenario: Implementing IT Governance in a High-Growth FinTech Environment
When payment platforms scale from regional to multi-country operations, they frequently face several pressures. Licensing and registration processes in new markets and winning banking partnerships are problematic and introduce a long list of compliance requirements, such as data residency rules and customer protection standards, to name a few.
Building a mid-scale SOC2 compliance infrastructure is a heavy lift as it touches every core workflow, from access management to vendor oversight. In practice, it involves re-engineering access logging architecture and building immutable audit trails to trace every privileged access and system change. This infrastructure work competes directly with product development for engineering capacity, forcing leadership to make trade-offs between near-term feature velocity and long-term market access.
Success in these scenarios usually depends on broken down silos. When leadership brings product managers and security leads to the same table during architecture reviews, risk decisions become tied to business timelines. Change management protocols built to satisfy banking risk committees eventually serve internal teams as a documented decision pathway that reduces incident resolution time.
How Beetroot Supports Your IT Governance and Risk Management Journey
The most difficult part is to define the path towards achieving digital resilience. You may know the theory of governance, but not everyone knows how to implement it and do so at the speed of your roadmap. Beetroot’s IT risk management consulting connects the framework to your operational reality by rooting roadmap decisions in the practicalities of the tech stack.
The biggest scope of work involves assessing the impact of governance gaps. Some may pose serious security vulnerabilities, while others may be in place solely for formality, yet they impact your delivery pace. We help organizations establish ownership models that clarify decision rights and structure IT project management practices with risk assessment embedded in architecture discussions.
The value of a partner lies in the ability to adapt governance to a particular technical context. Because a team scaling cloud infrastructure encounters different risks than one choosing an AI IDE for the next deployment. As a delivery-aware partner, we provide advisory support and connect enterprises with specialists who are as technically-versed as they are fluent in business-critical objectives.
The Path to Digital Resilience
If your IT governance and risk management framework can withstand the weight of its own complexity without stretching delivery timelines, you can safely say that it’s effective. This alignment is the ultimate hallmark of digital resilience. And the path to it starts from recognizing that your stack and your commercial goals are two sides of the coin.
The challenges on the road to accountable delivery are natural, and overcoming them with the right expertise will save you months of corrective work later. If you’re navigating similar trade-offs in your environment, we’re always open to comparing notes on effective governance models.
FAQ
Which IT governance frameworks are commonly used in enterprises?
Enterprises widely use several industry-leading frameworks to standardize their response to IT risk and ensure that technology investments align with business objectives. The most common frameworks are NIST CSF, ISO 27001, SOC 2, COBIT, and COSO, each addressing different governance dimensions.
How often should organizations update their IT risk assessments?
Organizations should update their IT risk assessment at least annually or whenever significant changes happen in the technical environment. The key is to regularly review the risk profile to ensure the governance framework remains relevant and effective.
Who should be responsible for IT governance in an enterprise organization?
Enterprise organizations should assign primary responsibility for IT governance to a cross-functional steering committee that includes executive leadership, the CIO, and representatives from key business units. Beetroot advocates an ownership model in which decision rights are clearly distributed between senior stakeholders and technical practitioners.
Does strong IT governance slow down innovation?
Modern IT governance accelerates innovation by replacing bureaucratic paperwork with faster and more informed decision-making frameworks that reduce organizational risk. Effective governance models empower organizations to take calculated risks by providing the necessary visibility and guardrails.
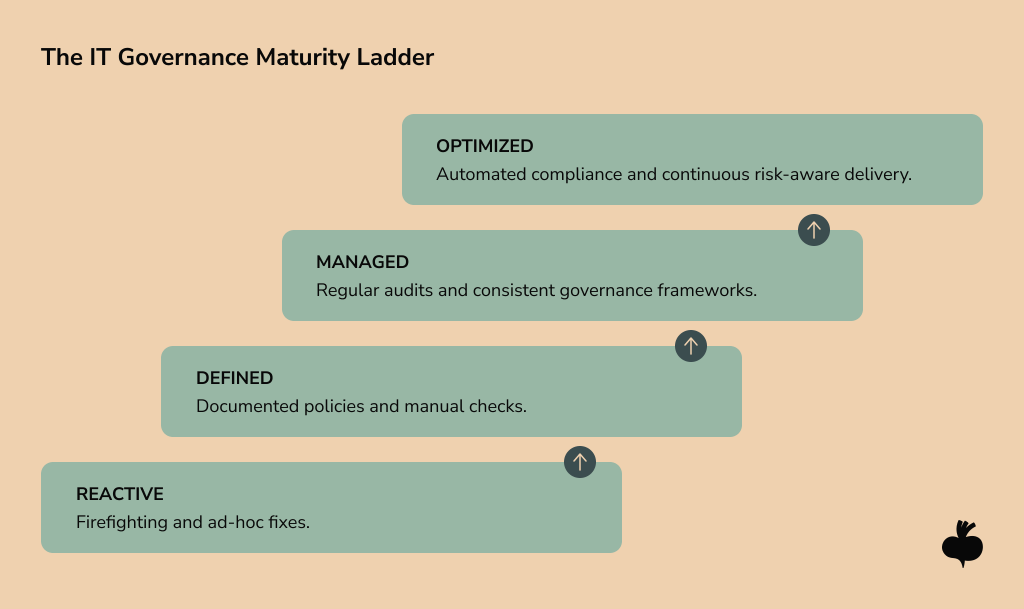
How can enterprises assess the maturity of their IT governance practices?
Enterprises evaluate the maturity of their IT governance practices using COBIT or CMMI models, which provide scales to measure process consistency and risk management. The assessment process benchmarks current operational habits against industry standards to determine how effectively technical decisions support the broader commercial strategy.
Subscribe to blog updates
Get the best new articles in your inbox. Get the lastest content first.
Recent articles from our magazine
Contact Us
Find out how we can help extend your tech team for sustainable growth.